Blog
AI-Accelerated Exploit Development Is Collapsing the iOS Security Model
Spencer Parker, Chief Product Officer

When Anthropic announced Claude Mythos Preview, a new frontier AI model, it did not position it as a typical product release. Instead, it published a detailed technical disclosure explaining why the model will not be made generally available. Read it, and the reasoning becomes clear.
The technical disclosure demonstrated the capability of frontier AI systems to identify previously unknown vulnerabilities in major operating systems, web browsers, cryptography libraries, and virtual machine monitors. These AI systems can build working exploits autonomously, including a full remote code execution chain against FreeBSD that requires no human intervention after an initial prompt. They can also chain multiple Linux kernel vulnerabilities into local privilege escalation exploits on fully hardened systems.
In short, the company determined that releasing this capability broadly, before defenses could be prepared, would cause more harm than benefit. This decision highlights a massive shift in the threat landscape that goes beyond any single model.
The AI Warning
Two numbers from the disclosure stand out regardless of what happens with Mythos Preview specifically, revealing the new reality of exploit development:
Turning a publicly disclosed vulnerability into a working exploit now takes mere hours.
The cost of building a full exploit chain can be under $2,000.
The same work previously required days to weeks from skilled, specialized researchers.
Again, these are not isolated results tied to a single AI model. They reflect where the capability frontier is today and where it is heading.
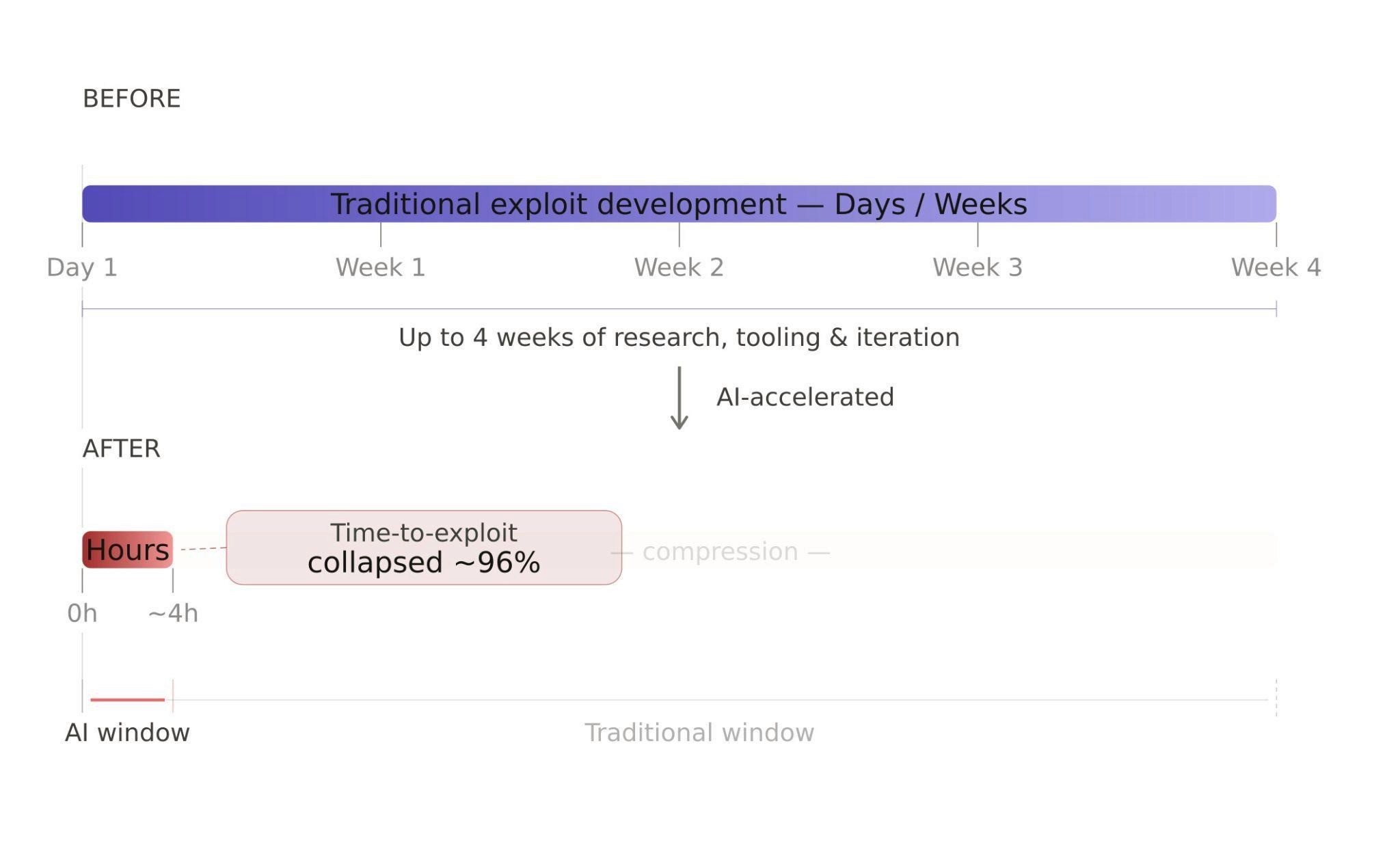
Even before the democratization of fuzzing capabilities fundamentally shifted the security landscape, Google’s recent stats already showed time to exploit collapsing to just days. Some analysts reported an average of -1 day, meaning exploitation often occurred before patches were even available.
The combination of thousands of legacy exploits and a supercharged exploit development cycle has collapsed the security window. This shift means IT teams are no longer responding to a periodic threat cadence; they are confronting a continuous one, which imposes an unsustainable pressure for immediate, continuous patching.
Windows/macOS: The EDR Advantage
For most enterprise endpoints, the security industry has spent twenty years building tooling that operates independent of patch status.
EDR platforms collect system-level telemetry from managed laptops and servers, giving security teams visibility into exploitation activity even on unpatched systems. A threat actor weaponizing a known vulnerability against a Windows or macOS endpoint faces a detection layer that does not depend on whether the patch has been applied.
This is not a complete answer to AI-accelerated exploit development. Patch cycles still matter.
Anthropic explicitly recommends shortening patch enforcement windows and treating dependency updates that carry CVE fixes as urgent rather than routine. But the detection layer provides meaningful time and visibility. An exploited endpoint that is monitored is a recoverable incident. The response capacity exists.
The calculus, however, is fundamentally different for iOS, which lacks this independent detection layer, a critical gap that turns a mobile compromise into a pathway for lateral movement.
The iOS Exception
Apple's mobile security model is architecturally coherent and, in many respects, technically strong. The walled garden approach combines hardware-backed security, a curated app review process, OS-level sandboxing, and tightly controlled update distribution. It is a deliberate design that has worked well against a broad class of threats.
The model has two dependencies.
Apple must identify and patch vulnerabilities before they are widely exploited.
Users must adopt those patches quickly.
AI-accelerated exploit development puts pressure on both.
On the first, Apple's security team is well-resourced, but AI systems are now capable of finding thousands of previously unknown vulnerabilities across major software projects in weeks, using automated scaffolding at relatively low cost. They have also demonstrated the capability to reverse-engineer closed-source binaries to identify vulnerabilities without access to source code.
To put this into context, a traditional iOS major version (like iOS 18) addressed an average of 180 bugs per year across its six primary patch cycles (averaging 30-40+ vulnerabilities per patch). The AI’s capability represents an order-of-magnitude increase in vulnerability discovery.
The competitive question for Apple is no longer whether its internal research can outpace a small number of elite researchers. It is something more difficult.
Can Apple fuzz at scale faster than the whole world? That is now a serious question, not a rhetorical one.
On the second: user adoption has always been the weaker dependency.
Historically, Apple’s security story was successful because only expensive commercial spyware successfully targeted their devices, and these were highly targeted. However, this changed significantly in 2026 with the disclosure of mass-targeting exploit kits such as Corona and DarkSword, which forced Apple to issue emergency patches for older, long-out-of-support iOS versions.
iVerify's research around the DarkSword exploit kit found that up to 25% of iPhone users were running OS versions vulnerable to the attack because they had not updated, or could not. In a 10,000-employee organization, that represents roughly 2,500 potential devices carrying a known, weaponizable vulnerability.
In a prior environment, the gap between disclosure and reliable exploit gave those users time. That gap is now measured in hours, a timeline that spells catastrophic failure for enterprises relying on user updates.
The Critical Detection Gap
The compounding problem is that iOS, unlike Windows or macOS, does not have an independent detection layer available to enterprise security teams. Apple restricts the deep system-level access required for most third-party Endpoint Detection and Response (EDR tools, leaving businesses uniquely dependent on Apple’s native security posture to defend themselves.
This constraint creates a critical visibility gap: businesses generally cannot use their own tools to detect exploits in real time, but must instead wait for an official patch, while employee devices are potentially being silently exploited.
Third-party applications on iOS operate inside strict sandboxes that limit access to system-level telemetry. This is the architectural decision that keeps malicious software from operating at depth on iOS. It also constrains what security software can observe.
Most organizations have implemented a Mobile Device Management (MDM) system that verifies OS version and policy compliance. It does not detect exploitation.
An unmonitored, compromised device becomes an undetectable beachhead, enabling lateral movement into the wider network. A device that is actively compromised can report a clean security posture to every tool in the enterprise stack.
Questions Apple Has Not Answered
AI augmentation means a fully working 0-day iOS exploit chain will no longer command $30M+ prices. Instead, users of these exploits will be far less careful in deployment. They will not care if they are "burned" quickly, exposing the entire framework to threat researchers and other adversaries. This effectively enables "God mode" for offensive cybersecurity companies, who will hold onto potentially hundreds of working exploit chains and sell them to access brokers for the highest bidder.
The AI acceleration of exploit development makes a set of questions about Apple's enterprise security commitments more urgent. They are not new, but they are now unavoidable.
Does the speed of AI directly counter Apple's go-it-alone security strategy? Apple's model assumes its internal security research capacity is sufficient to stay ahead of the threat landscape. AI tools available to any researcher at a low cost have changed that equation materially. The math no longer favors a platform that chooses to go it alone; it’s Apple vs. the rest of the world.
Can Apple fuzz at scale faster than the whole world? Adversaries leveraging Mythos-class models can identify and chain zero-day vulnerabilities at a pace that will likely exceed Apple’s internal security audits. Closed-source software is not immune to AI-driven vulnerability discovery. Reverse engineering of closed-source binaries is a documented capability in the Anthropic disclosure, meaning the scale advantage that Apple's architecture once provided is narrowing.
Even if Apple can keep pace, can enterprises react at the required speed? If the exploit development window has collapsed to hours, the implied patching cadence to keep pace approaches continuous. A weekly cadence is already untenable for many enterprise environments. A daily one is not a realistic operational posture.
What is Apple's plan for enterprises that cannot patch at that cadence? Apple backported patches to older OS versions for both Coruna and DarkSword, extending coverage to devices that could not run the current release. That is a meaningful step. However, the question is whether backporting becomes a systematic, sustained commitment, and whether Apple's security engineering capacity is scaled to support it at the volume AI-accelerated discovery is likely to require.
Thoughts from iVerify CPO, Spencer Parker:
"Opening up the iOS operating system to security vendors is the first step. Microsoft doesn't secure Windows alone -- CrowdStrike and others exist precisely because no single vendor can adequately defend its own platform at enterprise scale. Apple takes a different approach on iOS than it does on macOS, and that gap is now a liability. There are ways to extend visibility to third-party security tools that fully preserve Apple's privacy commitments. We'd welcome that conversation.”
What Enterprises Should Do Now
Defenders must adapt immediately, as the capability shift driven by AI models is already underway. Across the broader stack, this means:
shortening patch enforcement windows
treating CVE-bearing dependency updates as urgent
building detection and response tooling into every endpoint category, including the ones that have historically been treated as secondary concerns
For enterprise security teams, the most practical and urgent response is to close the existing mobile detection gap, regardless of how Apple's questions resolve.
For enterprises that traditionally operate on an N-1 or N-2 update cycle to ensure stability, this "patch-or-perish" pressure is fundamentally disruptive, forcing a choice between maintaining system uptime and leaving the front door wide open.
Out-of-cadence patches are also hugely expensive for a company and can create chaos. This has created a “stability vs. security” paradox that few enterprises are prepared to solve.
To address this, iVerify provides operating-system-level visibility into iOS and Android devices through log and artifact analysis. This capability identifies indicators of exploitation, spyware activity, and anomalous OS behavior that neither MDM nor the operating system surfaces. Detection operates independently of patch status, and deployment does not require MDM.
Apple's walled garden has been the foundational assumption of enterprise mobile security for 15 years. However, AI-accelerated exploit development has turned iOS into one of, if not the weakest and most dangerous endpoint in an organization, posing the most significant stress test that assumption has faced.
The lack of an independent detection layer means a compromised mobile device is an unmonitored beachhead for lateral movement across the network. This is no longer a matter of pressure; it’s a mandate. To manage risk effectively, enterprises must adopt the following strategic mandates:
Abandon N-1: Transition to an “N-0” patching strategy for iOS, as the risk of a broken app is now lower than the risk of a Mythos-class data breach.
Zero-Trust Networking: Move security to a zero-trust model where mobile devices are continuously monitored for kernel-level compromise before corporate data access is granted (i.e., adoption of mobile EDR).
Hardware Lifecycle Compression: Older devices lacking hardware-level memory protections (older than iPhone 15/16) must be retired from the fleet immediately, as they lack the silicon-level defenses needed to slow down AI-generated exploits.
Enterprises that continue to treat iOS as a solved security problem, managed by MDM and secured by the OS vendor, are carrying a detection gap that the current threat environment cannot afford. And this analysis doesn't even consider the fact that many phones in a corporate environment are personally owned (BYOD), meaning businesses have very limited visibility into the security of those devices.
AI has dissolved the security window; iVerify provides the independent detection layer required to operate safely in this new, continuous threat environment. Book a demo to learn more.
Subscribe to our blog to receive the latest research and industry trends delivered straight to your inbox. Our blog content covers sophisticated mobile threats, unpatched vulnerabilities, smishing, and the latest industry news to keep you informed and secure.