
Today, Google's Threat Intelligence Group published findings on what they've named "Coruna," a powerful iOS exploit kit containing 23 exploits across five full exploit chains targeting iPhones running iOS 13 through 17.2.1.
Over the past several weeks, iVerify researchers have been conducting independent technical analysis of this same exploit kit, tracking infrastructure, analyzing payloads, and mapping the exploit chain, including discovery of the delivery infrastructure. Our research corroborates and extends what Google has published. Coruna is one of the most significant examples we've observed of sophisticated spyware-grade capabilities proliferating from commercial surveillance vendors into the hands of nation-state actors and ultimately mass-scale criminal operations. Furthermore, it confirms what iVerify has long argued: the mobile threat landscape is not standing still, and the tools once reserved for targeting heads of state are now being deployed against ordinary iPhone users.
iVerify hosted a town hall on March 3. Register to view the recording, or contact us for a private briefing.
Here's what we found.
Background
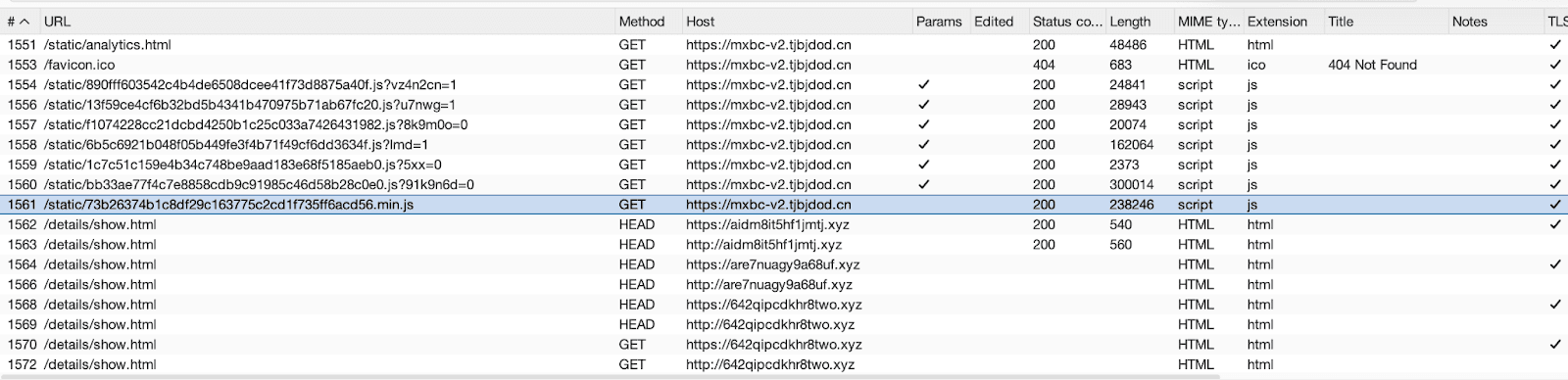
A couple of weeks ago, we discovered a suspicious looking domain mxbc-v2[.]tjbjdod[.]cn. On accessing the domain with an iPhone on iOS 16, we observed that the domain hosted a set of exploits on https://mxbc-v2[.]tjbjdod[.]cn/static/analytics.html. Over the course of the last week, we extracted as much of the exploits and implants as possible. The obtained 1-click exploit chains consists of Remote Code Execution (RCE) in Safari and a Local Privilege Escalation (LPE) exploit allowing attackers to take control over infected devices. Internally, we called the exploit kit CryptoWaters as it contained a set of modules targeted at cryptocurrency wallets and deployed as a waterhole attack. The same exploit chain was also observed by Google Threat Intelligence Group and called Coruna, and used by a Russian Threat Actor in Ukraine. See their blog for details.
In this blog post, we will share a high-level overview of the chains, including IOCs on how to find the attack on a device and via forensic acquisition. See the IOCs at the bottom of the post. The investigation and analysis still continue, and we aim to share more in the coming weeks.
Methodology
We focused our analysis on static, dynamic, and forensic analysis. In order to capture the different parts of the chain, we prepared multiple devices with custom root certificates and routed the traffic through a proxy. This allowed us to capture the different stages of the exploit and their C2 communication afterwards. We infected different devices between iOS 15 and 17. Our analysis in this blog post will follow one of the exploit chains found, but we have seen the same behavior on the other devices. Both arm64 and arm64e devices were infected. We took forensic snapshots of the devices before the infection, partly during and after we rebooted the device to remove the infection. The following forensic sources were gathered
Crashlogs
Sysdiagnoses
HTTP Communication (via Proxy)
Encrypted Backups
Full File System Dumps (for the devices that had a jailbreak available)
You can see in the following picture an overview of the attack.
The exploit chains did not contain any specific targeting or one-time links. Anyone who would have gone to the website with a vulnerable iOS version could get infected. This is not typical for targeted attacks used by nation-states, but rather e-criminal groups. We were able to reinfect our devices multiple times.
You can see in the following picture an overview of the attack. As reported by Google TIG, this framework is created in a modular way, and we have similar components here.
File Name | Component | Launched In |
|---|---|---|
analytics.html | loader | WebContent |
890fff603542c4b4de6508dcee41f73d8875a40f.js | WebKit JIT Exploit Trigger | WebContent |
13f59ce4cf6b32bd5b4341b470975b71ab67fc20.js | dyld shared cache parser to prepare for PAC bypass and LPE | WebContent |
f1074228cc21dcbd4250b1c25c033a7426431982.js | PAC Bypass + Native Code Exec | WebContent |
6b5c6921b048f05b449fe3f4b71f49cf6dd3634f.js | Encrypted code blob | WebContent |
1c7c51c159e4b34c748be9aad183e68f5185aeb0.js | Encrypted code blob | WebContent |
bb33ae77f4c7e8858cdb9c91985c46d58b28c0e0.js | LPE | WebContent |
73b26374b1c8df29c163775c2cd1f735ff6acd56.min.js | Stage 2 | powerd |
new.js | Stage 3 | locationd |
Multiple Different .js Files | Implant Modules | imagent, SpingBoard, WhatsApp, … |
During the device compromise process, different components of the exploit chain run validation checks:
The initial stage of the Safari Remote Code Execution (RCE) exploit is checking for:
Running in context of Apple iOS - Navigator.platform, navigator.maxTouchPoints, window.TouchEvent property.
Running in context of Safari (in specific version) - navigator.userAgent (AppleWebKit, Version), WebSQL support.
LockdownMode presence: IndexDB, MathML operations.
The Local Privilege Escalation (LPE) exploit is checking for:
Presence of Corellium virtualized iOS environment. Exploit is checking for the presence of the "/usr/libexec/corelliumd" file. We have not observed other checks related to forensics tools, research environment, or jailbreaks.
Crashlogs related to its previous activities. Once the crashlog is found it’s removed. Crashlogs of interest:
"com.apple.WebKit.WebContent"
"powerd"
"panic"
powerd and panic are interesting here. powerd because it is not directly involved in exploitation but used as a host for the first implant and panic because those would be resulting in a restart of the device and it would have to be re-exploited. So the chains clearly try to clean-up previous unsuccessful exploitation attempts.
Once the LPE is completed it will load 73b26374b1c8df29c163775c2cd1f735ff6acd56.min.js
inside powerd. This can be considered a second stage implant. This implant checks in with a command and control server. (In our case: aidm8it5hf1jmtj[.]xyz) It starts first with an HTTP HEAD message and subsequently retrieves a config file from /details/show.html. It then loads a new implant from the same domain (/details/new.js). The new component is the third stage which will be executed inside of locationd. Within its code this implant is referred to as CorePayload.
The third stage in locationd will start regular check-ins with a new domain uawwydy3qas6ykv[.]xyz. Additionally it will also retrieve the same configuration from aidm8it5hf1jmtj[.]xyz and additional modules. These modules depend on the installed apps on the device. The configuration contains a list of all available modules. In any case, the locationd implant will load modules for imagent (sms.js) and SpringBoard (helion.js). The implant will check if the targeted process is currently running and if yes it will inject the module into it. All of these modules are dylib’s. And none of them are code signed.
The imagent module takes over the C2 communication part and will also start to communicate with uawwydy3qas6ykv[.]xyz. It has a backup option that will allow them to communicate via SMS / iMessage. It appears locationd stops C2 communication at this point in time.
The SpringBoard component is not directly communicating with the C2 Servers, but has a communication channel to the locationd implant.
The locationd implant is not just the CorePayload for downloading other modules and orchestrating them, but it also contains modules to inspect photos and notes on the device. It will look for pictures and Apple Notes and upload them.
Similar to what GTIG posted on their blogpost we were able to retrieve the configuration files and the included modules. But we can see that these modules and the Coruna Exploit Kit are in active development. In our case we also had modules for imagent and WhatsApp. A full list of the captured modules and the decrypted config file can be found at the bottom of this post.
Most of the modules will either use a process dependent user agent or the following static one which does not relate to the iOS version of the device to communicate to their C2 servers.
User Agent:
Mozilla/5.0 (iPhone; CPU iPhone OS 16_0 like Mac OS X) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/16.0 Mobile/15E148 Safari/604.1
The process dependent user agent will be formatted like the following:
User Agent:
{process-name}/{version-process} CFNetwork/{version-CFNetwork} Darwin/{version-Darwin}
Detecting Coruna / CryptoWaters Infections
The Exploit Kit and implant leave behind plenty of traces. We won’t be able to detail all the behavior in this blogpost.
A first detection is using static User Agent and the process based User Agent to detect the sample in HTTP traffic. Both processes imagent and powerd do not communicate over the network with User Agents observed in the malware samples. The combination of different user agents for the same process (locationd), with different iOS versions in them is also suspicious. Additionally some Apps like WhatsApp have their own User Agent which would be different from the dynamically generated one. We have a list of all the User Agents at the bottom of this post.
During the execution the exploits and implants will create many files on disk. Some like:
/private/var/tmp/pl.sp.exec.guard.lock
which are temporary and deleted on reboot. Other files like:
/private/var/mobile/Library/Preferences/com.apple.photolibraryd.plist
stay persistent and are even backed up in an encrypted iTunes backup. There are other files which you can also investigate with access to the Full File System. To the best of our knowledge this file does not normally exist on iOS devices.
Additionally you can find evidence of the infection URL in Safari’s Browser History which will be included in an encrypted backup as well. You might be also able to find evidence of powerd and imagent inside of OSAnalyticsADDaily.plist, DataUsage.sqlite, netusage.sqlite and Powerlogs. The first two are also contained in a backup, while the latter two are only available on the full file system.
As this malware does not launch its own implant process but injects itself into other processes, there is no evidence of a dedicated process to look for. But it will launch dedicated threads and dispatch_queue’s with specific names like
plasma_supervisor or com.plasma.heartbeat.callback .
These can be found in stacks files (contained in iOS Analytics files), crashlogs or a spindump inside of sysdiagnose.
Finally there are also a couple of dedicated log messages that are indicating an infection with Coruna like:
failed lookup: name = com.plasma.springboard.ipc, flags = 0x1, requestor = locationd[69], error = 3: No such process
Other log messages will be depending on the behavior of the implants inside the processes rather than direct evidence.
Finding imagent doing a TLS request using the following format string in combination with imagent and powerd and com.apple.WebKit.Networking as the logging process would be evidence of it:
%{public}s(%d) %{public}s[%p] TLS configured [min_version(0x%04x) max_version(0x%04x) name(%{public}s) tickets(%{bool}d) false_start(%{bool}d) enforce_ev(%{bool}d) enforce_ats(%{bool}d) ech(%{bool}d)]
Final words
As this is the first time that mass exploitation against iOS devices has been observed in the public, we wanted to share as many IOCs as we can to support detection. Our investigation will continue and we will share more once we can. We are also providing a dedicated stix2 file for MVT. You can also use the iVerify Basic App to check for indicators there. We have made the app free to give everyone the chance to do so.
Organizations looking to monitor and protect their entire mobile fleet can book a demo of iVerify Enterprise to see how it detects sophisticated mobile threats like Coruna in real time.
Process Based IOCs - Process Behavior
Thread Names
IOC | Module | Comment |
|---|---|---|
plasma_core_heartbeat_receiver | powerd | Sysdiagnose, stacks.ips |
plasma_supervisor | locationd | Sysdiagnose, stacks.ips |
plasma_unified_dispatcher | locationd | Sysdiagnose, stacks.ips |
plasma_unified_ipc | locationd | Sysdiagnose, stacks.ips |
plasma_heartbeat_monitor | locationd | Sysdiagnose, stacks.ips |
helion_ipc_handler | locationd | Sysdiagnose, stacks.ips |
helion_ipc_handler | SpringBoard | Static Analysis |
Dispatch Queues
IOC | Module | Comment |
|---|---|---|
com.plasma.servervalidator.cache | imagent | Static Analysis |
com.plasma.springcore.messagesend | SpringBoard | Static Analysis |
com.plasma.heartbeat.callback | locationd | Static Analysis |
com.plasma.event.upload.serial | locationd | Static Analysis |
com.plasma.corepayload.springboard.retry | locationd | Static Analysis |
com.plasma.notes.monitor | locationd | Static Analysis |
com.plasma.appruntime.scheduler.configwork | locationd | Static Analysis |
com.plasma.appruntime.scheduler | locationd | Static Analysis |
com.plasma.appruntime.scheduler.download.counter | locationd | Static Analysis |
com.plasma.appruntime.scheduler.recovery | locationd | Static Analysis |
com.plasma.appruntime.scheduler.heartbeat | locationd | Static Analysis |
com.plasma.bundlemapper.concurrent | locationd | Static Analysis |
com.plasma.bundlemapper.refresh | locationd | Static Analysis |
com.plasma.appruntime.modulestore | locationd | Static Analysis |
com.plasma.applistreporter.periodic | locationd | Static Analysis |
com.plasma.systemstatusreporter.periodic | locationd | Static Analysis |
com.plasma.photomonitor | locationd | Static Analysis |
com.plasma.photomonitor.processing | locationd | Static Analysis |
com.plasma.photomonitor.retry | locationd | Static Analysis |
com.plasma.appruntime.downloadmanager | locationd | Static Analysis |
com.plasma.appruntime.netconfig | locationd | Static Analysis |
com.plasma.appruntime.appdiscovery | locationd | Static Analysis |
com.plasma.PLProcessStateDetector | locationd | Static Analysis |
com.plasma.servervalidator.cache | locationd | Static Analysis |
com.plasma.appruntime.hotupdatemanager | locationd | Static Analysis |
com.plasma.appruntime.hotupdatemanager.download | locationd | Static Analysis |
com.plasma.appruntime.hotupdatemanager.io | locationd | Static Analysis |
com.plasma.appruntime.hotupdatemanager.state | locationd | Static Analysis |
com.google3xm.fucimt77p | io.metamask.MetaMask | Static Analysis |
com.google3.fucimt77 | im.token.app | Static Analysis |
com.google.decff.queue | com.tronlink.hdwallet | Static Analysis |
com.google1.fuc7788 | com.jbig.tonkeeper | Static Analysis |
com.google2.fuc676 | org.mytonwallet.app | Static Analysis |
hook.passcode.decrypt.queue | org.mytonwallet.app | Static Analysis |
com.balance.memmove.log | com.solflare.mobile | Static Analysis |
com.blockChat.timer.queue | net.whatsapp.WhatsApp | Static Analysis + Forensic Data |
com.plasma.servervalidator.cache | All Modules | Static Analysis |
Log Messages
IOC | Process | Component | Comment |
|---|---|---|---|
failed lookup: name = com.plasma.springboard.ipc, flags = 0x1, requestor = locationd[69], error = 3: No such process | launchd | UnifiedLogs | Depends on locationd’s pid. |
%{public}s(%d) %{public}s[%p] TLS configured [min_version(0x%04x) max_version(0x%04x) name(%{public}s) tickets(%{bool}d) false_start(%{bool}d) enforce_ev(%{bool}d) enforce_ats(%{bool}d) ech(%{bool}d)] | com.apple.WebKit.Networking | UnifiedLogs | Will contain the original exploit server domain. The format string itself is normal behavior for com.apple.WebKit.Networking |
%{public}s(%d) %{public}s[%p] TLS configured [min_version(0x%04x) max_version(0x%04x) name(%{public}s) tickets(%{bool}d) false_start(%{bool}d) enforce_ev(%{bool}d) enforce_ats(%{bool}d) ech(%{bool}d)] | powerd | UnifiedLogs | Format String. Event Message will contain the domain if it was not privacy redacted. |
%{public}s(%d) %{public}s[%p] TLS configured [min_version(0x%04x) max_version(0x%04x) name(%{public}s) tickets(%{bool}d) false_start(%{bool}d) enforce_ev(%{bool}d) enforce_ats(%{bool}d) ech(%{bool}d)] | imagent | UnifiedLogs | Format String. Event Message will contain the domain if it was not privacy redacted. |
Data Usage for %@ on flow %llu - WiFi in/out: %@/%@, WiFi delta_in/delta_out: %lld/%lld, Cell in/out: %@/%@, Cell delta_in/delta_out: %lld/%lld, RNF: %d, subscriber tag: %@ | symptomsd | UnifiedLogs | Format String. Event Message contains imagent. |
FLOW %@ | symptomsd | UnifiedLogs | Format String. Event Message contains imagent or powerd. |
entry: %@ %41@%s %12@ %12@ %12@ %12@ %3@ %3@ | symptomsd | UnifiedLogs | Format String. Event Message contains imagent or powerd. Entry in netusage.sqlite |
AppTracker for %@ flows: self %d others %d prev %d %d traffic rx %lld tx %lld avg duration %f rx %lld tx %lld everset 0x%x bitmap %@ | symptomsd | UnifiedLogs | Format String. Event Message contains imagent or powerd. |
Can't lookup UUID %{public}@ for procname %{public}@, coalition %{public}@ nehelper %{public}@ | symptomsd | UnifiedLogs | Format String. Event Message contains imagent or powerd. |
Stall symptom %@: added unique stall type (%lu) on interface type (%ld) for new process %@ | symptomsd | UnifiedLogs | Format String. Event Message contains powerd. |
Stall symptom detail: (symName/procName/ePid/ifIndex/interfaceType/stallType/endpoint/isFgOrBg): %@/%@/%d/%d/%ld/%lu/%{private}@/%@ | symptomsd | UnifiedLogs | Format String. Event Message contains powerd. |
iftype=%s ifIndex=%d bundle=%s procName=%s eprocName=%@ pid=%lld epid=%lld EUUID=%@ endpoint=%{private}@ | symptomsd | UnifiedLogs | Format String. Event Message contains powerd. |
%{public}@ Ignoring GPU update because this process is not GPU managed | runningboard | UnifiedLogs | Format String. Event Message contains powerd, imagent. |
%{public}@ Ignoring jetsam update because this process is not memory-managed | runningboard | UnifiedLogs | Format String. Event Message contains powerd, imagent. |
%{public}@ Ignoring memory limit update because this process is not memory-managed | runningboard | UnifiedLogs | Format String. Event Message contains powerd, imagent. |
Network Based IOCs
IOC | Module | HTTP Method | Comment |
|---|---|---|---|
Mozilla/5.0 (iPhone; CPU iPhone OS 16_0 like Mac OS X) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/16.0 Mobile/15E148 Safari/604.1 | powerd | GET | User Agent used by multiple implants / modules. |
PowerManagement%20configd%20plugin/{version} CFNetwork/{version} Darwin/{version} | powerd | HEAD | User Agent - iOS Version Dependent |
imagent/{version-imagent} CFNetwork/{version2} Darwin/{version3} | imagent | GET, POST | User Agent - iOS Version Dependent |
Mozilla/5.0 (iPhone; CPU iPhone OS 16_0 like Mac OS X) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/16.0 Mobile/15E148 Safari/604.1 | locationd | User Agent used by multiple implants / modules. | |
locationd/{version-locationd} CFNetwork/{version2} Darwin/{version3} | Second Implant | HEAD, GET | User Agent - iOS Version Dependent |
WhatsApp/{version-WhatsApp} CFNetwork/{version2}Darwin/{version3} | GET, POST | User Agent - iOS and App Version Dependent | |
MetaMask/{versionMetaMask} CFNetwork/{version2} Darwin/{version3} | MetaMask | GET | User Agent - iOS and App Version Dependent |
ProcessName/{versionProcess} CFNetwork/{version2} Darwin/{version3} | Generic | GET, POST | Generic User Agent |
IOCs available inside Backups
IOC | Module | Comment |
|---|---|---|
Infection Domain + URL | Safari History.db | |
/Library/Preferences/com.apple.photolibraryd.plist | Manifest.db | Relative Path for Home Domain |
98be59db1ad60b6e6e9e9d43442ce1e9e0e17b65 | Manifest.db | File ID in Manifest.db |
C2 Domains | <Safari Domain>/Library/WebKit/WebsiteData/ResourceLoadStatistics/observations.db |
File Based IOCs
IOC | Module | Available In | Comment |
|---|---|---|---|
/private/var/tmp/pl.sp.exec.guard.lock | powerd | FFS | Temporary |
/private/var/tmp/pl.core.lock | locationd | FFS | Temporary |
/private/var/tmp/upgrade.dylib | locationd | FFS | Temporary (Static Analysis) |
/private/var/tmp/relaunch | locationd | FFS | Temporary (Static Analysis) |
/private/var/tmp/reinstall | locationd | FFS | Temporary (Static Analysis) |
/private/var/tmp/stop | locationd | FFS | Temporary (Static Analysis) |
/private/var/mobile/Library/Preferences/com.apple.photolibraryd.plist | locationd | FFS | Persistent |
HomeDomain - Library/Preferences/com.apple.photolibraryd.plist - 98be59db1ad60b6e6e9e9d43442ce1e9e0e17b65 | locationd | Backup | Persistent |
/private/var/mobile/Library/Caches/.com.apple.notes.cache.plist | locationd | FFS | Persistent |
/private/var/mobile/Library/ Caches/.com.apple.mobileassetd.cache | locationd | FFS | Might be persistent |
/private/var/mobile/Library/Preferences/com.apple.photolibraryd.retry.plist | locationd | Backup | Based on Static Analysis |
/private/var/root/Library/Caches/com.apple.nsurlsessiond/fsCachedData0E1A3DC1C51C2D879DE016E56D3EECE8 | locationd | FFS | Config - might be depending on the Chain. |
/private/var/root/Library/Caches/com.apple.WebKit.WebContent/blob_d6c1a21adb11f0ea023b9a35 | locationd | FFS | Persistent, maybe different per device. |
Components Overview
Macho Files Exploit Phase
File Name | Stage | sha256_file | minos | sdk |
|---|---|---|---|---|
1f2b15ec991f963e02dce6e586fc2c07f8893914.macho | Exploit | 31494c96cd890ab4d93f62d84f2cb273936df3ffbaacaa13bb0e318ffb16a692 | 13 | 13 |
24cc1e2131b42a5044e49368313520618bad48a2.macho | Exploit | 79c27dccb899af47ea7900e4f6ab5dc3312a53ef0b6c3a7ded535dc6f2755ee2 | 13 | 13 |
3073fa1f9a1d744683f8d2bbe00308c01c774e9d.macho | Exploit | 3f57d5057092f9a6e340f8497be9402660d78f307c6a481f7f757cfd7fe5149c | 13 | 13 |
621e10ba92ba23ea56d553daa24d347e3f4f4e0e.macho | Exploit | ef9169cde76d8d41008c8efa9828483633b117651087c8722e459fa1c173e0da | 13 | 13 |
8403aea68afc338764bae9fb9f9d239ee60d1013.macho | Exploit | a12a7a8db91f1e364f43b3d695d9f58172f2b168f29488f593714e255cf500d4 | 13 | 13 |
8737367f47627791d0da62e2f6af73a1eda0e5c8.macho | Exploit | 067c2c99ef0b537fb9ca9de9beed8ad1a01faa68c021a82d935c52fb7211c411 | 13 | 13 |
8bb1ec9f85d7d425d03daf753b0cae2f6fb9f554.macho | Exploit | 946da0bef24d50655a2d9177611ec4c11929dda375805bf4272806491c4e34cc | 13 | 13 |
a9e44fd116082895c7c47f37291d4c41af00cd3e.macho | Exploit | 9ac0454100f1409b1984d3133db1eb0a121381f9d5969121f8eabf3970eac51e | 13 | 13 |
aacea6aadd112fdc82bfc61a1e2e31ae211bf5b9.macho | Exploit | ae67f7a235061643b64625c2c3cd125c6a5559d772c4c6a1aa8d6d19998bec9a | 13 | 13 |
b9b8db765426578396475573808568e63f1fe12f.macho | Exploit | a986c15401fda1d9ad7e4b308e4907dced24e30d2126fac8f7c788dda049455d | 13 | 13 |
bb33ae77f4c7e8858cdb9c91985c46d58b28c0e0.macho | Exploit | f84e13161729ff8b9f46ad4d77a09273c790f808dd9b1298ecf23eb54efa939c | 13 | 13 |
c73ca2dca0217836f1b8ff50eb94b973fbdf8776.macho | Exploit | f214717c4222b89bc4f0d45b1cf9166f38bfe9daa7361d326e653fcc6c77518c | 13 | 13 |
f3722237ebcd1984b45aa90309de2a423127e4ac.macho | Exploit | 03417453be0a3045a2fccb3ae4124623d8478ead976e6468b85da142400546ad | 13 | 13 |
27cfb7407d9dd8e063f0d3074901f1d68dd0f0d5.macho | Exploit | 63b6b3181822df175fdb4b58a08703be5bbfd18fc38612dc8396df0dbd2c0f09 | 14 | 14 |
4e6c09d98a1bf7908820e9887346a0e74e1f70f9.macho | Exploit | 14746193252a44d2c2f251cdc20400ebcf9f96cd90a22c4c50c9816cd80c68f9 | 14 | 14 |
52568339c794b5ccede75453af7f355c902926cd.macho | Exploit | a938b812696e8b01830423cd05d3b60defbaebd5b65e62aa87501884e8acc209 | 14 | 14 |
5f00845b09a7b799438f5d3441bbd37fc471f691.macho | Exploit | d2e8d45a52e1788cf679d15c3a3f89e7428c5958557c19964e7cd59f7fe802f4 | 14 | 14 |
f6a8e01da61ee19857072f626a01ad6bf1a7d7ed.macho | Exploit | ce11b285b4226979c1cfe50a119feff3df66e11d8a1e2f10a680ef2d6c63cb07 | 14 | 14 |
Core Modules
File Name | Implanted Process | sha256_file | minos | sdk | @0_lc_id_dylib |
|---|---|---|---|---|---|
helion.js | SpringBoard | 73390742eba6f7a85d894f961efa77272fbaceb91a278efcad4f497612c02699 | 13 | 16.2 | @rpath/helion.dylib |
new.js | locationd | 3ef82e94d38bbc44626f3821db9eda2ea636c1ae413d8890b752bd965acd2c6e | 13 | 16.2 | /usr/local/lib/CorePayload.dylib |
0371be6951227616286c593e3c588ecff7d58f90.min.js | powerd | 9dfa3fa7e81993174669bedb08b3212993e91d93d6227f0cf8b8d45b6981a9c0 | 13 | 16.2 | /usr/local/lib/SamplePayload.dylib |
73b26374b1c8df29c163775c2cd1f735ff6acd56.min.js | powerd | bed840be5744726f8d344b4aca51508a673cce77368c78023bd0c17f29df5c78 | 14 | 16.2 | /usr/local/lib/SamplePayload.dylib |
sms.js | imagent | cb8ee5920b7dcc1d16a71342a21adfb7423363427110f66198b94964c87ec547 | 14 | 18.2 | libSMSBroadcast.dylib |
Implant Modules
File Name | Bundle Id | sha256_file | minos | sdk | @0_lc_id_dylib |
|---|---|---|---|---|---|
a1lib.js | io.metamask.MetaMask | 612cb971bd84f005bc10ac701293b0f80ebafd25b51e7ba6d541df2d536f5e69 | 15 | 18.2 | @executable_path/Frameworks/libaaDylib.dylib/libaaDylib.dylib |
b2lib.js | im.token.app | 1e86532642e13027cf77f32e50ee1314e2bf35015c4556085fc2eba7e6b8d6d8 | 15 | 18.2 | @executable_path/Frameworks/libbbDylib.dylib/libbbDylib.dylib |
f6lib.js | com.bitkeep.os | 4c2d67afd451badc642db9ee188972217718c399ac999a83e20e4501229d22d3 | 15 | 18.2 | @executable_path/Frameworks/libbitDylib.dylib/libbitDylib.dylib |
d4lib.js | com.sixdays.trust | b0b6c50df15e1e99c4d23da002b29f31a648a7bab9831283d6306cc7a60bdd42 | 15 | 18.2 | @executable_path/Frameworks/libddDylib.dylib/libddDylib.dylib |
c3lib.js | com.tronlink.hdwallet | e7b06484763ee379c969613fbfe73bab29f1a0836ae2208136df564596354a04 | 15 | 18.2 | @executable_path/Frameworks/libffDylib.dylib/libffDylib.dylib |
e5lib.js | orgjstoshi.distribution | b541840d71f466c249422012fc0e91f0c90a35c9759bb791e721567cdb773cb1 | 15 | 18.2 | @executable_path/Frameworks/libffDylib.dylib/libffDylib.dylib |
j10lib.js | org.mytonwallet.app | 2b90b95338f4f928eaccbaa6bbd6a5283def5ec9bf97e2902c4d2a3f7e502649 | 15 | 18.2 | @executable_path/Frameworks/libffDylib.dylib/libffDylib.dylib |
m13lib.js | com.kyrd.krystal.ios | 6715b1be1c0b35fe82cce71eb224db32205df9bb53e55083d592b711f16d008f | 15 | 18.2 | @executable_path/Frameworks/libffDylib.dylib/libffDylib.dylib |
n14lib.js | com.tonhub.app | 2daa9dc9cedda40b2b0793bdc38314e8f2e694ebf10f27bf2fb45030af9b538a | 15 | 18.2 | @executable_path/Frameworks/libffDylib.dylib/libffDylib.dylib |
s19lib.js | com.solflare.mobile | 9cfcdc594e2d5c4d4eefe4e5a967d90096eedfd352c89c87ed81c716aca25966 | 15 | 18.2 | @executable_path/Frameworks/libffDylib.dylib/libffDylib.dylib |
g7lib.js | com.jbig.tonkeeper | b541840d71f466c249422012fc0e91f0c90a35c9759bb791e721567cdb773cb1 | 15 | 18.2 | @executable_path/Frameworks/libggDylib.dylib/libggDylib.dylib |
h8lib.js | com.uniswap.mobile | 6d8cfa2a73f5ef754e2ae5ba83b7b4f0588cbe1bb1d2970bf89bfaba954c9ff4 | 15 | 18.2 | @executable_path/Frameworks/libggDylib.dylib/libggDylib.dylib |
i9lib.js | app.phantom | cf2d1788cb336581dfbdd556eb77f983fca4b0d39250efbfe4f10b20214576e5 | 15 | 18.2 | @executable_path/Frameworks/libggDylib.dylib/libggDylib.dylib |
k11lib.js | exodus-movement.exodus | 0035f50f9adb9ba98ef1eb394724c3ff6cf7a4a26dc6e7662a1c9c95afa20ed1 | 15 | 18.2 | @executable_path/Frameworks/libggDylib.dylib/libggDylib.dylib |
l12lib.js | com.skymavis.Genesis | 7979c79f58b7316557cba7d0f49fac2c409010aa770fab74348e6d974d1ea244 | 15 | 18.2 | @executable_path/Frameworks/libggDylib.dylib/libggDylib.dylib |
p16lib.js | com.global.wallet.ios | d46c0d304370b4ca40526d029bce48e9912d8b5111cb6f4db359c769a951e8bb | 15 | 18.2 | @executable_path/Frameworks/libggDylib.dylib/libggDylib.dylib |
q17lib.js | coin98.crypto.finance.insights | 0d0e89b9a48c2471b00b2c47d81fc17b3b4a3c74414127a009b3f0658801181d | 15 | 18.2 | @executable_path/Frameworks/libggDylib.dylib/libggDylib.dylib |
r18lib.js | com.bitpie.wallet | 86dc5728538e67197d71f731c640652ebfb0b03b9da15d5ba78cbfa0aa9d8c4f | 15 | 18.2 | @executable_path/Frameworks/libggDylib.dylib/libggDylib.dylib |
t20lib.js | com.123.okex.OKExAppstoreFull | 80a056f8e12be600bb3c2b72fa90189d3aff4ac9798aa3ca10e266d34b84e5ba | 15 | 18.2 | @executable_path/Frameworks/libggDylib.dylib/libggDylib.dylib |
wap.js | c091e67ceebe869ec50eac32ed385d7d5043abd9c5dbcf2be65128f41a3cdf06 | 15.6 | 18.2 | @executable_path/Frameworks/mdTest.dylib/mdTest.dylib |
Observed Domains
Domain | Function | Comment |
|---|---|---|
mxbc-v2[.]tjbjdod[.]cn | Exploit Server | |
aidm8it5hf1jmtj[.]xyz | Config and Implant Server | |
uawwydy3qas6ykv[.]xyz | C2 Communication |
Config from /details/show.html we were able to decrypt
Subscribe to our blog to receive the latest research and industry trends delivered straight to your inbox. Our blog content covers sophisticated mobile threats, unpatched vulnerabilities, smishing, and the latest industry news to keep you informed and secure.




