In March 2026, the Google Threat Intelligence Group (GTIG) published details on the Coruna exploit framework. The subsequent news coverage focused mainly on the sophistication of the exploit chain.
The more important question is not just how Coruna works, but what companies should do about it. Because Coruna is not just a single threat, it’s a signal that mobile security risk has evolved beyond the assumptions most organizations still operate under.
Reset Assumptions
Many mobile security strategies are built on outdated beliefs. Coruna challenges nearly all of them.
The nation-state-grade exploit kit demonstrates that:
Advanced exploitation is no longer limited to high-value individuals
User interaction is no longer a reliable control point
Mobile devices can be compromised without malicious apps
Post-compromise activity can blend into legitimate system processes
If your current strategy assumes any of the above, it is already outdated.
However, the first step is not deploying new tools; it’s recognizing that mobile devices are now a primary attack surface, not a secondary one.
Shift From Management to Security
Most enterprise mobile programs are still centered on device management. Tools like MDM are essential for enforcing policy, but they were never designed to detect sophisticated threats.
Coruna makes that gap clearer than ever as the attack operates entirely outside the controls that management platforms are designed to enforce.
To address this gap, security leaders need to explicitly separate the two functions:
Device management, which focuses on configuration and compliance
Threat detection and response, which focuses on adversary activity
Treating these as interchangeable creates blind spots that can only be closed through investment in capabilities that go beyond just configuration enforcement.
Prioritize Visibility Across the Mobile Stack
Coruna is detectable, but only if you can see what is happening on the device.
The indicators identified by iVerify’s technical team span multiple layers:
Network behavior from system processes
File system artifacts, both temporary and persistent
Signals in backups, analytics logs, and system diagnostics
Cross-process activity and injection patterns
No single data source tells the full story, so effective detection depends on correlating signals across these layers. This is where most organizations fall short.
Mobile endpoints are often treated as opaque, with limited telemetry available for analysis, but without visibility, even well-understood threats remain invisible.
Focus Detection on Behavior - Not Just Indicators
Coruna includes identifiable indicators of compromise, but those indicators are not static. The framework is modular and actively evolving.
Relying solely on known domains, file paths, or hashes is not sufficient. Instead, detection strategies should focus on patterns such as:
System processes making unexpected network requests
Inconsistent or anomalous user agent strings
Unusual relationships between processes and network activity
Evidence of code injection into trusted services
These behaviors are harder for attackers to fully disguise and are more resilient to change over time.
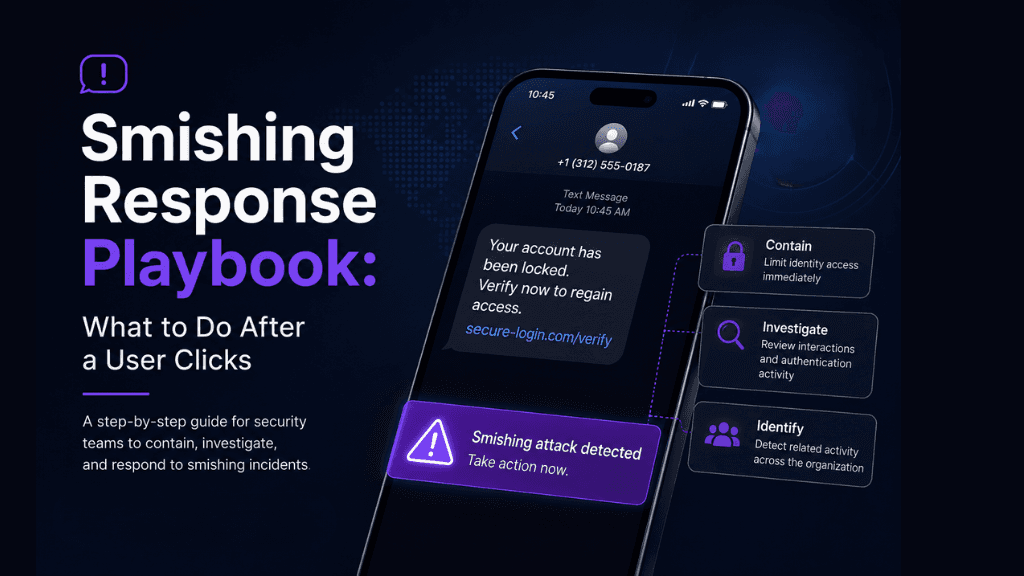
Define Mobile Incident Response Capability
Most organizations do not have a defined process for responding to mobile threats at this level.
When compromise occurs, the response is not as simple as removing an app or resetting a password. Security teams need to be able to:
Assess whether a device has been compromised
Collect and analyze forensic artifacts
Determine the scope of data exposure
Decide on appropriate remediation actions
This may include device replacement, credential rotation, and broader investigation into related systems.
Without a defined playbook, response efforts will be slow, inconsistent, and incomplete.
Align Mobile Risk With Enterprise Risk
One of the most persistent challenges in mobile security is not technical, but conceptual. Mobile devices are still often treated as peripheral endpoints, while laptops, servers, and cloud infrastructure carry most of the weight in enterprise risk models. In reality, they provide a direct pathway into the same identities, credentials, and systems that define enterprise risk.
When a mobile device is compromised, attackers can move through authentication tokens, session cookies, messaging apps, SSO integrations, and cloud-connected workflows to access organizational resources.
The phone is not the end target; it’s the entry point, and security leaders should ensure mobile is explicitly included in enterprise risk structures by:
Including mobile compromise scenarios in identity and access threat models
Representing mobile devices in business impact assessments alongside other critical assets
Treating token theft and session hijacking as primary enterprise attack paths
Integrating mobile telemetry into SOC workflows rather than isolating it in separate tools
This is not about elevating mobile for its own sake. It is about accurately reflecting how modern attackers move through enterprise environments.
Summary
Coruna is not an edge case. It is an early signal of how advanced mobile threats are evolving and how far most enterprise security strategies still have to go.
Security leaders who treat it as a one-off incident will remain in a reactive posture, responding to threats after the fact. Those who recognize it as a turning point have an opportunity to reassess assumptions, close critical visibility gaps, and build mobile security programs that reflect how modern attacks actually operate.
The question is no longer whether mobile devices are part of the enterprise attack surface. It’s whether your security strategy is equipped to defend them accordingly.
Looking for a tool that delivers the deep mobile visibility your organization needs to get ahead of the next Coruna? Book a Demo of iVerify Today
Subscribe to our blog to receive the latest research and industry trends delivered straight to your inbox. Our blog content covers sophisticated mobile threats, unpatched vulnerabilities, smishing, and the latest industry news to keep you informed and secure.