
When people search for the most common types of smishing, they’re usually expecting a list.
But in practice, smishing attacks don’t vary as much as people think. The same core patterns show up again and again, with small variations in wording or context.
What actually changes is how those patterns are adapted to feel relevant, urgent, and believable in the moment.
To understand the most common types of smishing, it’s more useful to look at the scenarios attackers reuse and the mechanics that make them effective.
Account Security Alerts (Suspension, Fraud, or Unusual Activity)
One of the most common smishing patterns is the account alert.
These messages typically claim that something is wrong: suspicious activity has been detected, a login attempt failed, or the account is about to be suspended. The message then provides a link or asks for a response to resolve the issue.
What makes this effective is the combination of authority and urgency.
The sender appears to be a trusted institution, often a bank or service provider, and the message creates a time-bound threat. Users are conditioned to respond quickly to legitimate alerts of this kind, so the behavior feels normal.
Because the message is short and direct, there’s little opportunity to question it. The decision becomes immediate: fix the issue now or risk losing access.
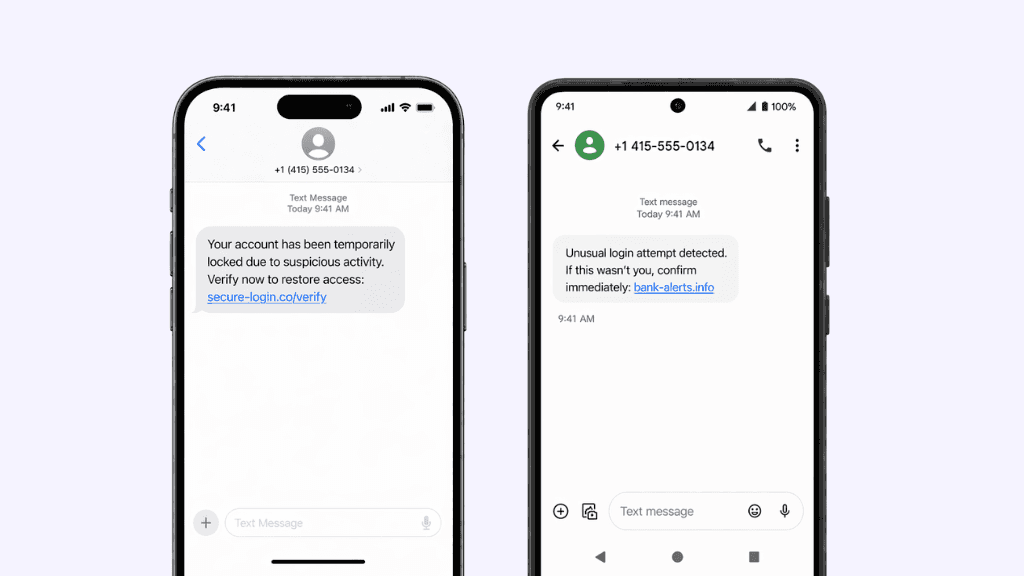
Example messages:
“Your account has been temporarily locked due to suspicious activity. Verify now to restore access: secure-login.co/verify”
“Unusual login attempt detected. If this wasn’t you, confirm immediately: bank-alerts.info”
Delivery and Service Notifications
Another very common category is delivery-related messaging.
These messages typically say that a package is delayed, a delivery failed, or additional information is needed to complete a shipment. They include a link to “resolve” the issue.
This works because it aligns with everyday expectations. Most people are frequently expecting packages or services, so the message doesn’t feel unusual.
There’s also a built-in sense of low-risk urgency. It’s not as severe as a financial alert, but it still encourages quick action to avoid inconvenience.
From an attacker’s perspective, this is a reliable pattern because it applies to a broad audience without needing much personalization.
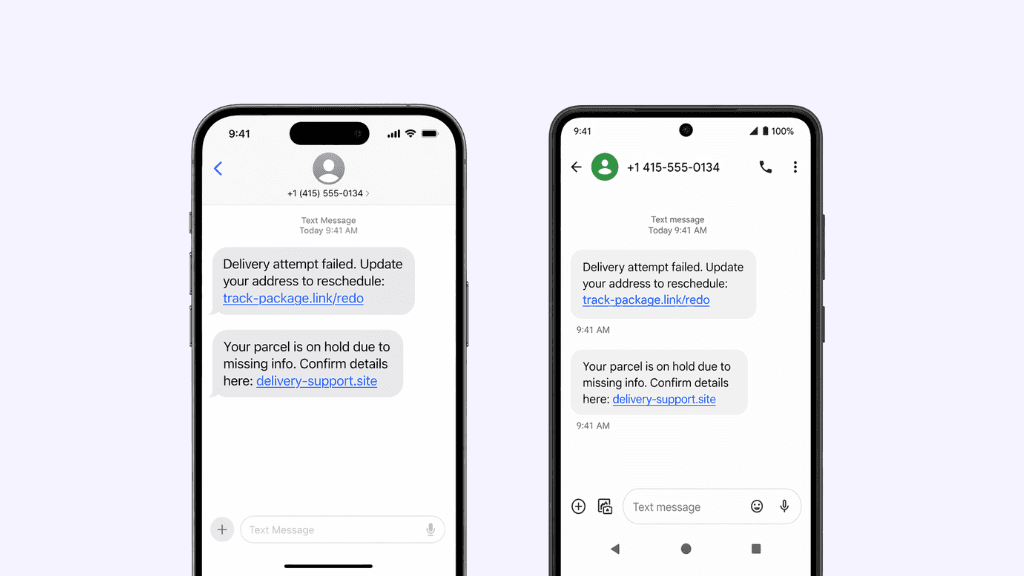
Example messages:
“Delivery attempt failed. Update your address to reschedule: track-package.link/redo”
“Your parcel is on hold due to missing info. Confirm details here: delivery-support.site”
Financial Institution Impersonation
Closely related to account alerts, but often more targeted, are messages that impersonate banks or financial services directly.
These messages may reference transactions, verification steps, or account access issues. They are typically very concise and include a single action, such as clicking a link or replying to confirm identity.
What makes these messages effective is recognition.
Users are used to receiving legitimate SMS messages from financial institutions, especially for things like one-time passcodes or fraud notifications. That familiarity reduces skepticism.
In many cases, attackers will also use shortened or slightly altered links that resemble legitimate domains. Given the limited visibility on mobile, users often don’t have enough context to distinguish between real and fake.
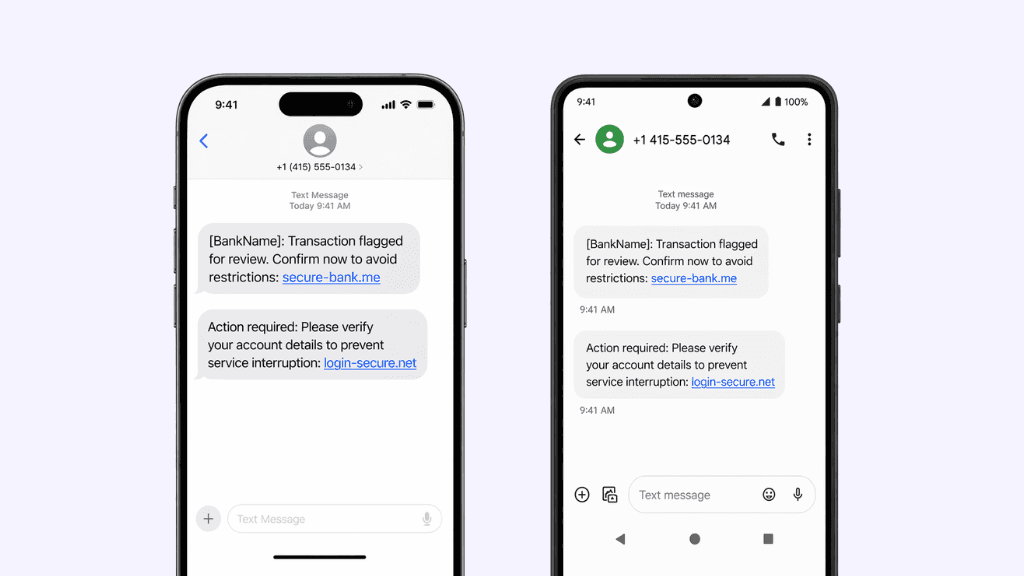
Example messages:
“[BankName]: Transaction flagged for review. Confirm now to avoid restrictions: secure-bank.me”
“Action required: Please verify your account details to prevent service interruption: login-secure.net”
Generic Urgent Action Messages
Not all smishing attempts rely on a specific scenario. Some are deliberately generic.
These messages focus almost entirely on urgency, with minimal context. They might say that immediate action is required, that access will be restricted, or that a verification step is needed.
The lack of detail is intentional.
In SMS, there is no expectation of long explanations. A short, directive message can feel legitimate simply because it matches the format users are familiar with.
This type of message relies on speed over specificity. The goal is not to convince the user through detail, but to prompt a quick reaction before they have time to question it.
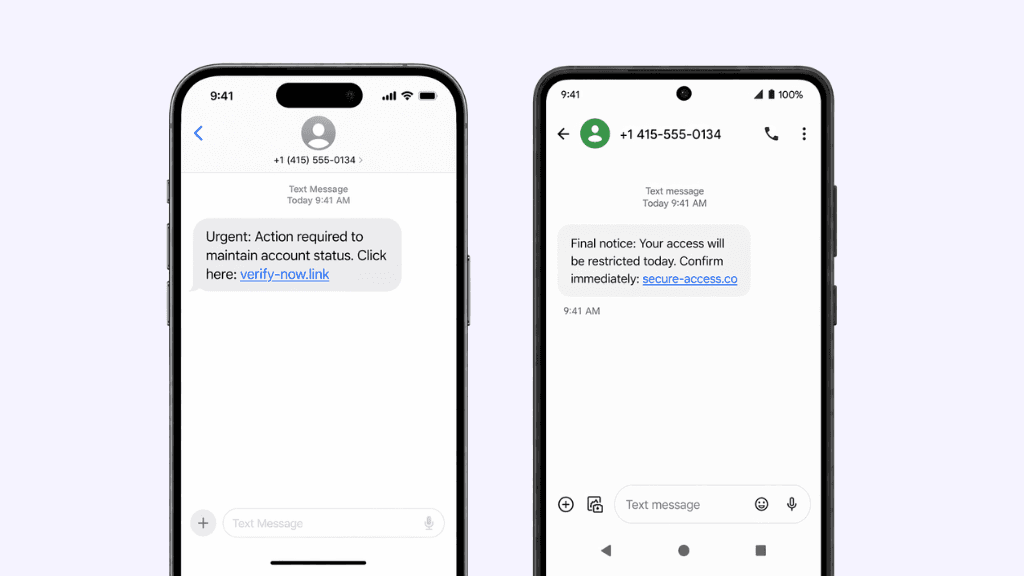
Example messages:
“Final notice: Your access will be restricted today. Confirm immediately: secure-access.co”
“Urgent: Action required to maintain account status. Click here: verify-now.link”
Personalized and Context-Aware Messages
Some smishing attacks incorporate elements of personalization.
This can include referencing a specific service, using a name, or aligning the message with recent activity. The level of personalization doesn’t need to be deep. Even a small detail can make the message feel more credible.
This is possible because a large amount of personal data is already available through breaches or public sources. Attackers can use that information to craft messages that feel more relevant to the recipient.
In a channel like SMS, where messages are already brief, that small increase in relevance can have a disproportionate impact on trust.
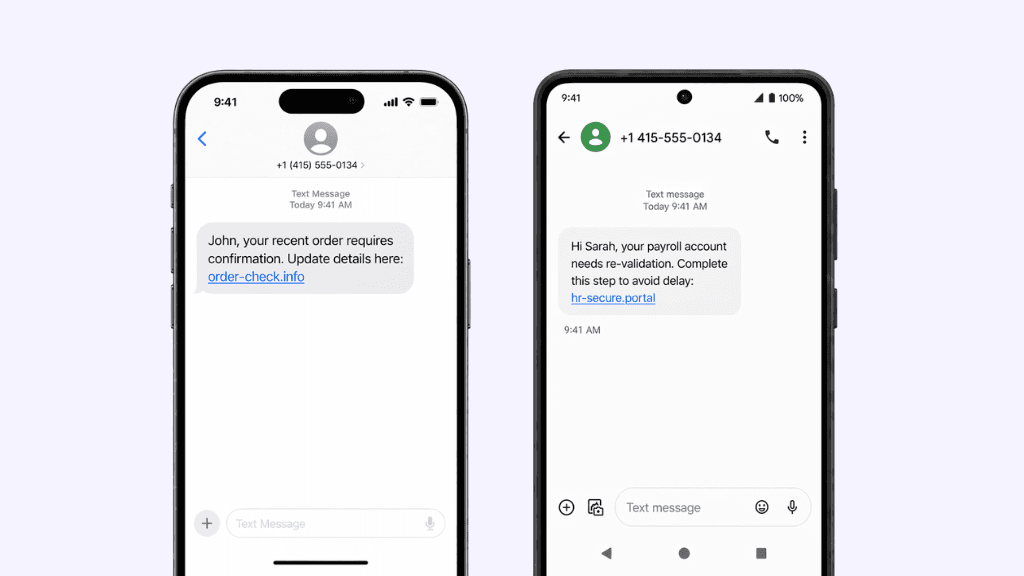
Example messages:
“Hi Sarah, your payroll account needs re-validation. Complete this step to avoid delay: hr-secure.portal”
“John, your recent order requires confirmation. Update details here: order-check.info”
What These Attacks Have in Common
Across all of these categories, the structure is very consistent.
A smishing message is typically
short
highly focused
built around a single action
framed with urgency and delivered with minimal context
There are no visuals to analyze, no headers to inspect, and no additional signals to rely on. The message is designed to move the user from notification to action as quickly as possible.
In that sense, the “type” of smishing matters less than the environment it operates in.
Why These Patterns Continue to Work
These patterns are effective because they align with how people already use SMS.
Text messages are expected to be short, direct, and actionable. They are often tied to important or time-sensitive events. And they are delivered on devices that people interact with quickly, often without full attention.
At the same time, the mobile environment limits the user’s ability to verify what they’re seeing. Links can’t be easily inspected, context is minimal, and interaction is immediate.
When you combine those factors, even simple messages become highly effective.
What This Means for Enterprise Security
For security teams, the takeaway is not just that these attack types exist, but that they are easy to replicate and difficult to distinguish from legitimate communication.
Because the patterns are so consistent and so minimal, traditional approaches like user training or rule-based detection are less effective. The signals those approaches rely on are either missing or significantly reduced in SMS.
That means the challenge is not just identifying specific types of smishing, but addressing the broader gap in visibility and control within the channel itself.
Subscribe to our blog to receive the latest research and industry trends delivered straight to your inbox. Our blog content covers sophisticated mobile threats, unpatched vulnerabilities, smishing, and the latest industry news to keep you informed and secure.




