Smishing attacks are 6-10 times more effective than email-based phishing. Not because attackers are doing something fundamentally new, but because SMS creates the right conditions for an attack to succeed. The channel itself reduces friction, limits visibility, and accelerates decision-making in a way email doesn’t.
To understand why, it helps to look at how users interact with SMS, and what’s missing from both a security and usability perspective.
1. Smishing Removes the Signals Users Rely On
Even non-technical users have learned to look for certain indicators when they receive an email that looks a little off. They might check the sender address, hover over a link, or notice a formatting issue or a logo that looks different. SMS doesn’t provide those signals.
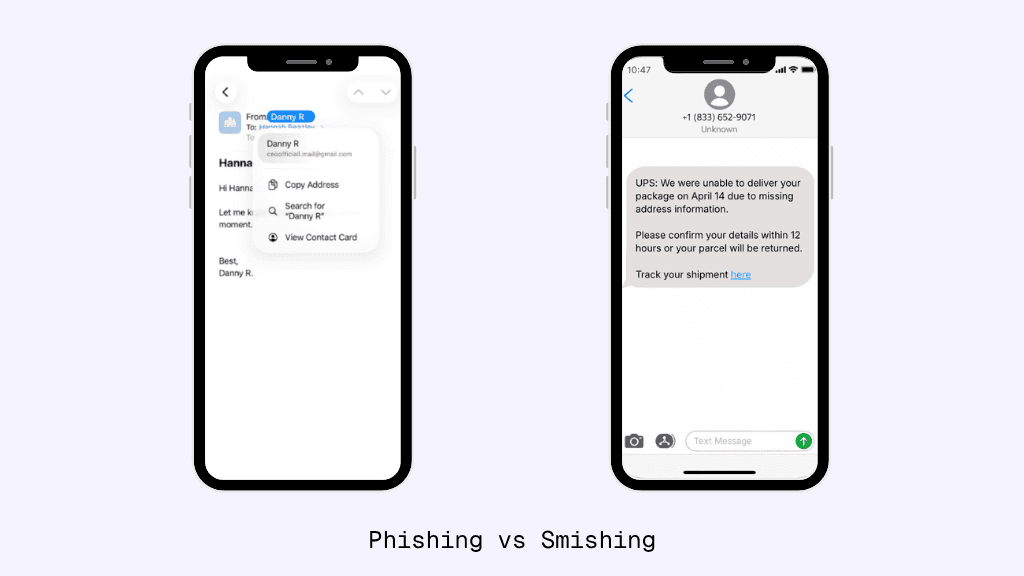
A text message is just a sender name or number and a short message. There are no headers to inspect, no formatting cues, and no visual indicators like logos or layout. There’s very little context to evaluate, and very little time spent evaluating it.
That absence of signal matters. It means users are making decisions with less information, not necessarily worse judgment.
2. The Mobile Experience Is Built for Speed, Not Inspection
On mobile, the interaction model is fundamentally different from desktop.
There’s no hover state to preview a link. URLs are often truncated, showing only part of the destination. Mobile browsers expose minimal context, and there are fewer ways to inspect what’s happening behind the scenes.
In many cases, users don’t even open the full message. They act directly from the notification or lock screen, where even less information is visible.
The result is a compressed interaction: receive, glance, act.
From an attacker’s perspective, that’s ideal. There is almost no friction between delivering the message and getting the user to engage with it.
3. SMS Is a High-Trust Channel by Design
One of the biggest differences between SMS and email is trust.
Text messages are commonly used for legitimate, time-sensitive communication. Banks send fraud alerts. Services send verification codes. Healthcare providers send reminders. These messages are short, direct, and often require immediate action.
Over time, users have been conditioned to trust that pattern.
If a message looks like it comes from a known institution and asks for a quick action, it aligns with what users already expect. There’s less reason to question it.
That trust isn’t accidental. It’s been built over years of legitimate use, and now attackers are reusing it.
4. Smishing Messages Are Engineered for Immediate Action
Smishing messages are designed very differently from phishing emails.
They are intentionally brief, often just a few lines, and focused on a single action. There’s no attempt to provide detailed context or explanation. Every word is there to move the user toward clicking a link or responding.
Urgency plays a central role.
A typical message introduces a problem—an account suspension, a failed delivery, a fraud alert—and then immediately provides a way to resolve it. The timeframe is short, and the action is simple.
That combination reduces the likelihood that a user will pause to validate the message. Instead, the decision happens quickly, often instinctively.
5. Tap-First Interaction Reduces Friction to a Single Step
Mobile devices are optimized for tap-based interaction.
Moving from a message to a link is a single action. There is no need to open a new application, navigate a browser, or perform multiple steps. Even compared to clicking a link in an email, the process is faster and more direct.
This “tap-first” design removes friction at exactly the point where security typically depends on it.
In many cases, users interact with messages while distracted, in motion, or multitasking. That further reduces the likelihood of careful evaluation.
6. Personalization Makes Smishing More Convincing
Another factor that increases the effectiveness of smishing attacks is how easy it is to personalize SMS messages.
Phone numbers are often tied to real identities, and personal data is widely available through breaches and public sources. That information can be used to craft messages that feel specific and relevant to the recipient.
Even small details, like referencing a bank, a delivery, or a recent activity, can significantly increase credibility.
Because SMS messages are short, personalization doesn’t need to be deep. A single relevant detail can be enough.
7. Security Controls Lag Behind the Threat
From a technical standpoint, SMS lacks many of the controls that help reduce phishing risk in email.
There is no standardized sender authentication, no consistent filtering layer, and no reliable way for enterprises to inspect messages before they reach the user. Attackers can rotate numbers and links quickly, often faster than any blocking mechanism can respond.
On the device itself, visibility is limited. Messages are not consistently logged or retained, and forensic investigation after an incident is difficult.
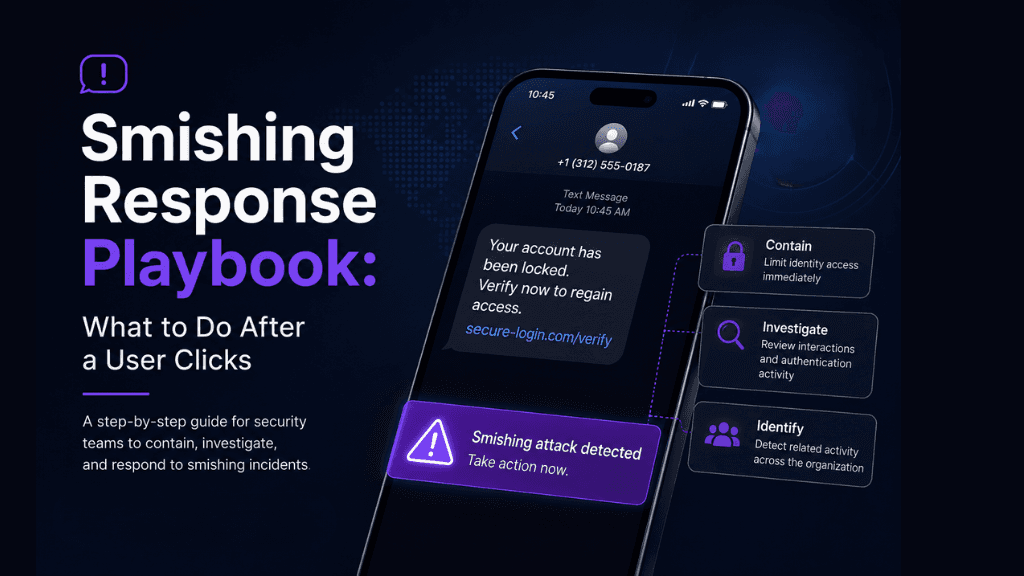
That combination means smishing attacks are not just more effective, they are also harder to detect and contain.
What This Means for Enterprise Security
For security teams, this creates a gap that traditional approaches don’t fully address.
Email security controls don’t extend to SMS, and user awareness training often assumes signals and behaviors that don’t exist on mobile. As a result, organizations are left with limited options for detecting or preventing these attacks.
Closing that gap requires rethinking how visibility and control are applied in a mobile-first environment, especially within channels like SMS that operate outside traditional security boundaries.
Subscribe to our blog to receive the latest research and industry trends delivered straight to your inbox. Our blog content covers sophisticated mobile threats, unpatched vulnerabilities, smishing, and the latest industry news to keep you informed and secure.